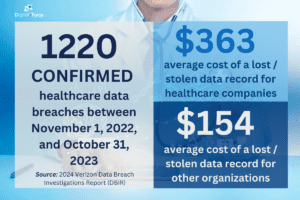
The healthcare industry has embraced cloud computing to drive agility, scalability, and cost efficiencies. However, using multi-cloud service providers (mCSPs) introduces complexities in consistently securing sensitive data across different platforms and architectures, impacting healthcare data security.
A fragmented multi-cloud approach can lead to gaps in security policies, inconsistent access controls, and a disjointed view of risks. Is there any hope for the healthcare industry? In this article, we highlight the best strategies for data protection in a multi-cloud setting and how the healthcare industry can benefit by implementing these strategies.
Healthcare Data Protection in a Multi-Cloud Environment
Healthcare organizations must implement robust governance and technical controls tailored to a multi-cloud environment.
Technical Challenges and Mitigation Tactics Data Encryption: Maintaining uniform encryption standards and key management processes is critical but challenging with diverse CSP encryption services and APIs. Healthcare organizations should standardize encryption libraries and algorithms that meet HIPAA/HITECH requirements. Leverage multi-cloud key management solutions and automate encryption of data at rest, in transit, and use across providers.
Identity and Access Management (IAM): Inconsistent IAM policies/tools increase risks of excessive data access or compromised credentials. Implement a centralized identity provider to enforce strong authentication like multi-factor (MFA). Federated identities across CSPs and cloud identity stores like AWS IAM. Enforce least-privileged access based on multi-cloud attribute-based policies. Automate provisioning/de-provisioning and audit effective permissions.
API Security: Cloud services integration via APIs expands attack surfaces. Deploy API gateways to monitor/secure client-provider traffic flows. Implement OAuth 2.0 and leverage WAFs to protect against vulnerabilities. Routinely discover/decommission shadow/unused APIs.
Data Loss Prevention (DLP): Distributed data across heterogeneous cloud storage increases DLP complexity. Unify discovery and classification of sensitive data across all data stores using CASB/CWPP tools. Automate monitoring for anomalous data transfers using UEBA. Enforce encryption, masking, and other controls on cloud data.
Cloud Security Posture Management (CSPM): With disparate cloud assets/policies across providers, leverage CSPM tools for continuous monitoring of multi-cloud risks, compliance, and misconfiguration. Implement centralized asset inventory and data governance. Use CSPM for unified policy enforcement and automated remediation.
Healthcare Data Security Governance and Strategy in a Multi-Cloud Environment
According to a Forbes Technology Council article, “A multi-cloud model can leave organizations open to major security risks from misconfiguration of policies” if not properly governed. Healthcare providers must establish a cloud security governance framework that extends across all CSPs with consistent policies, processes, and centralized oversight.
This includes developing a comprehensive multi-cloud security architecture, defining security and compliance requirements upfront, implementing risk management programs tailored to the distributed cloud footprint, and ensuring executive leadership and cross-functional collaboration.
A robust healthcare data security strategy founded on principles like least privilege, encryption everywhere, audit trails, and automated policy-based controls can help protect healthcare data in a multi-cloud environment. However, according to cybersecurity firm CrowdStrike, “Maintaining consistent security policy management and enforcement across multiple cloud platforms is the greatest operational challenge.”
To address this, implement standardized multi-cloud security solutions that provide centralized visibility, policy management, and automated enforcement across all cloud instances from a single pane of glass. This unified approach reduces misconfiguration risks through consistent implementation of security best practices.
DigitalXForce – Your “Digital Trust” Partner for Healthcare Data Security in Multi-Cloud Environments

At DigitalXForce, our suite of Integrated Risk Management solutions builds Digital Trust in multi-cloud environments and enables healthcare organizations to meet HIPAA regulations.
Here’s what we give you:
Attack Surface Management (ASM) and Asset Inventory
How can you identify, monitor, and manage digital assets across multi-cloud environments while gaining clear insights into your attack surface? Our robust attack surface management solution provides these capabilities, with the asset inventory module also serving as a safety net for meeting regulatory compliance requirements efficiently and providing evidence of due diligence during audits.
Real-time, Continuous Integrated Risk Management
Continuously monitor multi-cloud environments, gather threat intelligence, assess risks in real-time, automate mitigation, drive data-backed decisions, and foster a collaborative approach as part of your robust Cybersecurity program.
Automated Audit, Compliance, and, Risk Assessment
Automate data collection from sources, continuously monitor for risks and compliance gaps, provide centralized risk and compliance dashboards, map policies to regulations, prioritize risks via scoring, enable automated remediation, generate compliance reports, and integrate with GRC/SIEM tools.
DigitalX Risk Quantification and Prioritization
Identify potential risks by analyzing technology, processes, people, and the environment. Quantify risk likelihood and impact, and prioritize critical threats to align with organizational risk tolerance and appetite.
Automated DigitalX Security Posture Management
Unlike other GRC/IRM solutions out there, we provide automated assessments against standards, quantify and prioritize risks based on impact and likelihood, and enable automated remediation of issues.
Automated Security Blueprint Generator
Our security blueprint generator analyzes requirements, incorporates industry standards, and creates a customized security architecture that prioritizes critical risks. This feature integrates with existing infrastructure, automates implementation, enables continuous monitoring, and provides reporting to maintain compliance and enhance overall security.
Automated Board Metrics and Report Generator
This tool aggregates data, automates trend analysis, and provides visual dashboards. It enables custom metrics, offers tailored reports, and integrates with other systems, empowering leadership to make informed cybersecurity decisions and build resilient IT environments.
Automated Cyber Insurance Application Processor
The cyber insurance application processor collects data, conducts risk assessments, customizes rules, generates policies, tracks applications, and provides reporting. This speeds processing, tailors coverage, and ensures competitive premiums.
DigitalX Risk Remediation Planner
The risk management tool proactively identifies and assesses potential risks by integrating with security data sources. It quantifies and prioritizes risks using algorithms, generates tailored remediation recommendations, manages mitigation workflows, integrates with other systems, and offers reporting/analytics.
DigitalX Policy Reviewer and Generator
The policy management generator provides customizable templates aligned with standards, enables tailored policy creation, identifies non-compliant policies, tracks versions, integrates with systems, manages review tasks, and offers reporting/analytics.
DigitalX Security Management and Operations Plan Generator
This solution provides customizable plan templates aligned with industry standards, facilitating tailored plans for organizational needs and compliance. It integrates with other systems, manages security task workflows, tracks plan versions, and offers reporting/analytics on effectiveness and compliance.
Third-Party Risk Management
DigitalXForce centralizes and manages vendor data, contracts, and assessments, evaluating vendor risks with “Digital Trust” scores. It benchmarks vendors against compliance frameworks, alerts on risks, monitors continuously, generates reports, and shares actionable risk plans for collaboration.
Key Takeaways
As healthcare data proliferates across a heterogeneous multi-cloud landscape, maintaining a strong security posture is paramount:
- Establish centralized governance, policies, and oversight of the entire multi-cloud estate
- Leverage cloud-agnostic security solutions for consistent encryption, IAM, DLP, and monitoring
- Automate security response and enforcement through policy-as-code and cloud security orchestration
- Unified CSPM provides continuous compliance and misconfiguration remediation across providers
- Executive leadership and cross-functional collaboration is critical for an effective multi-cloud strategy
- The DigitalXForce comprehensive integrated risk management solutions enable robust security strategies, compliance maintenance, proactive risk mitigation, streamlined vendor management, and data-driven decision-making for multi-cloud environments used by organizations in the healthcare industry.
By proactively addressing the technical and governance challenges and utilizing outcome-based integrated risk management solutions like DigitalXForce, healthcare organizations can navigate the complexities of the multi-cloud environment while ensuring the protection of sensitive data assets.
 DigitalXForce strengthens trust and security with SOC 2 certification, demonstrating robust data protection, privacy practices, and operational excellence in delivering cutting-edge digital solutions for clients across industries.
DigitalXForce strengthens trust and security with SOC 2 certification, demonstrating robust data protection, privacy practices, and operational excellence in delivering cutting-edge digital solutions for clients across industries.